Malwarebytes 4.6.4.286 Crack With Activation Key

Malwarebytes Crack bytes developed a software named malware bytes. In the beginning, it was well known as malware bytes anti-malware. Malware byte is malware opposing software. You can use this software on Microsoft Windows and IOS devices. You can use this software free of cost. Smartphones can be secured from mobile adware using this software. You can separate viruses even using the free version of this software. The free version also enables you to scan viruses. The paid version of malware bytes gives you organized scans. It also gives you a flash memory scanner.
Malware bytes are accessible in many languages. This software protects you from illegal access to your data. It detects and separates spyware in actual time with modern anti-malware. It enables you to scan future dangers. You can also scan horrible dangers using this software. You can keep safe your system from weak programs. These soft programs may cause impurity. You can use malware bytes on Windows XP, IOS 11, and Android Jelly Bean. This software for Android keeps away malware and is harmless on your PC and tablets. You can identify harmful applications for your system. Malware bytes software has user-friendly interaction.
Malware byte is much more secure software. You can use this software safely. You can get rid of all junk files using this software. It enables you to hide your place and calls. You can also hide your activities using this software. It enables you to scan the untruthful safety program.
Moreover, you can also scan adware and distrustful material. You can use this software very quickly and simply. It is also useful for MS anti-virus malware.
Key Features:
- Shield Security: Malware bytes software gives a shield to chosen programs from assaults.
- Secure software: Malware bytes software eliminates the mess that spyware makes. It enables you to secure your material and network. You can also keep secure workers.
- Multiple devices: This software gives you multiple devices to protect your system.
- Cybersecurity: Malware bytes software offers much more effective security for Mac.
- Guaranteed privacy: This software blocks scam activities and provides guaranteed privacy for IOS. You can make your IOS device harmless and faster than before.
Uses:
- You can use this software to find malware of all types. However, you can also remove malware of all types using this software.
- You can use malware bytes to avoid hackers. You can also avoid infections and distrustful websites using this software.
- This software is for social interaction with others. Nobody can trace and steal your content.
- This software is also used to keep safe files from locking.
What’s New?
- The most recently released version of this software is malware bytes 4.6.4.286.
- It is very useful for hypervisor code reliability.
- It provides you with the accuracy of web security.
- You can increase reliability using this latest version.
- It also makes good remediation processes using the most recent version of malware byte.
A Full Organazied Software:
A reputable cybersecurity company, Malwarebytes is well-known for its comprehensive anti-virus and malware solutions. The Malwarebytes programming suite is intended to safeguard PCs and cell phones against many dangers, including infections, malware, ransomware, spyware, and possibly undesirable projects (Puppies). Advanced scanning algorithms are used by Malwarebytes to find and remove a variety of malware types, providing comprehensive protection against both established and emerging threats.
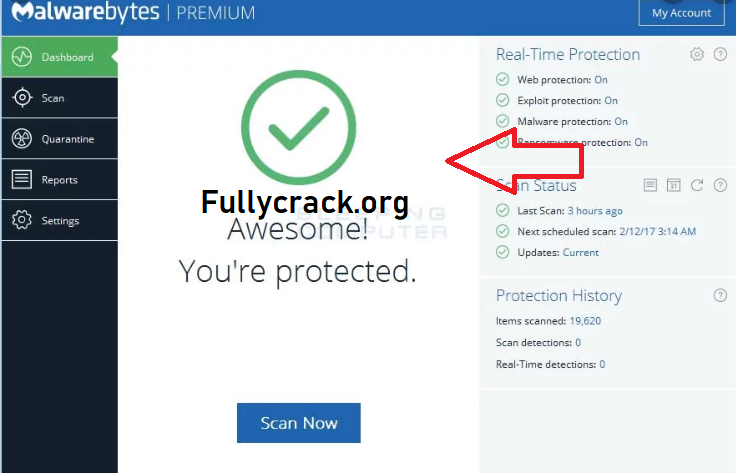
By continuously monitoring system activity, the software provides real-time protection, preventing malware infections and blocking harmful websites or links before they can harm. Malwarebytes has specialized protections against ransomware attacks that stop files from being encrypted and prevent sensitive data from being held hostage.
It safeguards users from phishing attempts, malicious websites, and browser-based attacks at the browser level, ensuring a safer online browsing experience. Clients can perform custom sweeps of explicit envelopes or drives, considering designated malware location. Scheduled scans can also be set to run at particular times or intervals.
Mirror File